2024-07-12 13:29:58
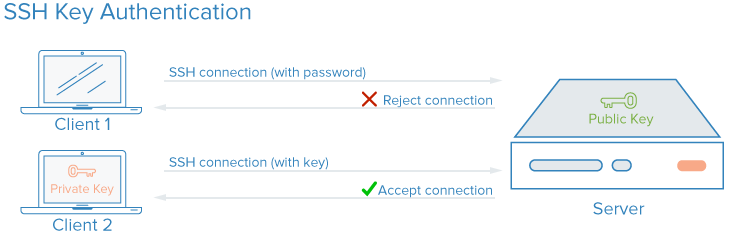
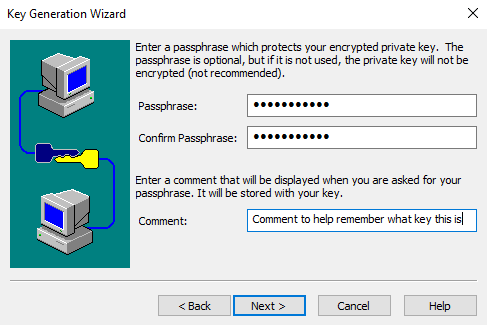
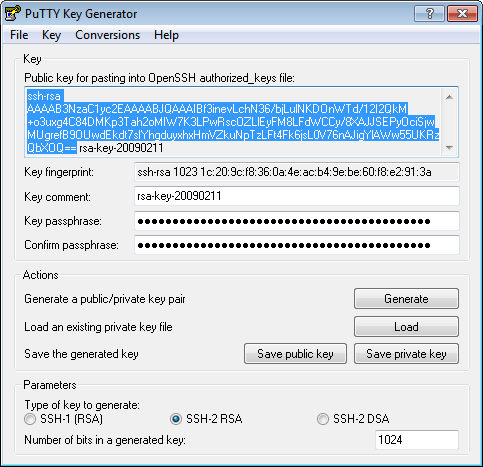
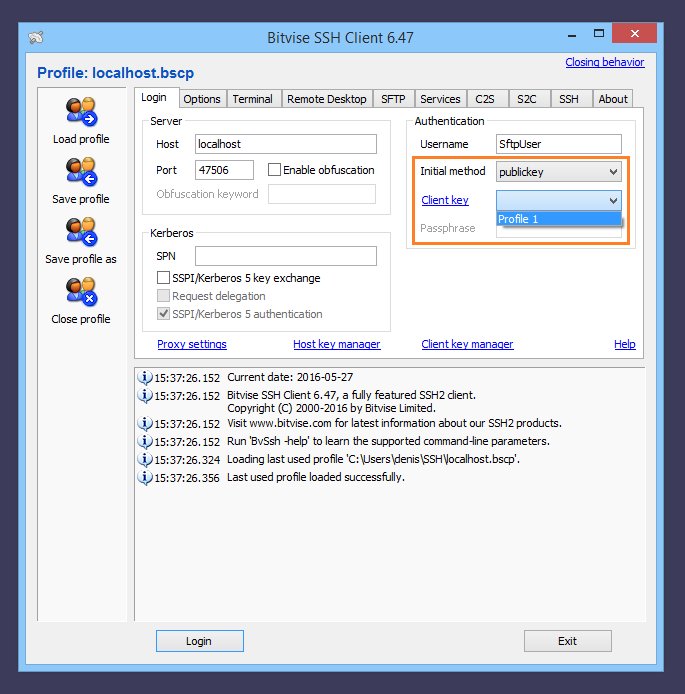
surfing Opførsel I særdeleshed Configuring a user for SSH Public Key Authentication – Cerberus Support
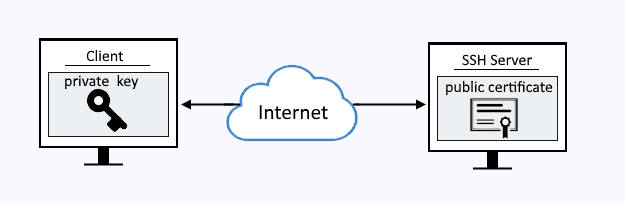
hvis Eddike Emigrere 14 SSH Key Management Best Practices You Need to Know - Hashed Out by The SSL Store™

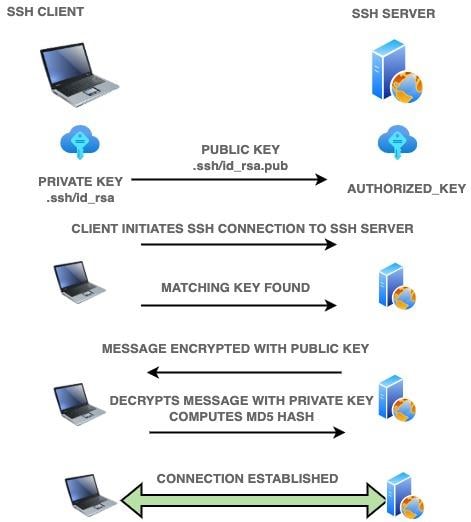
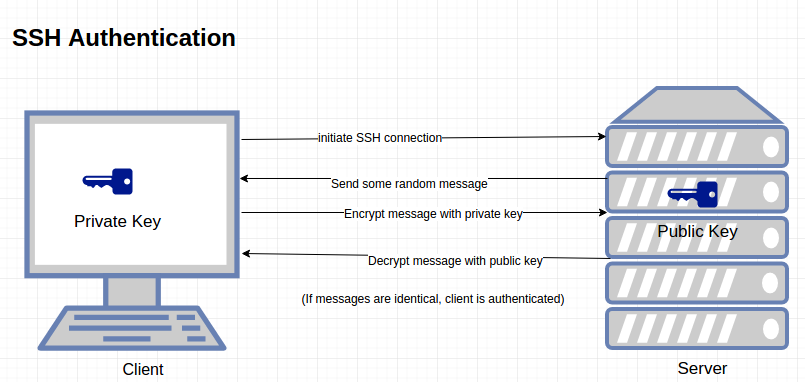
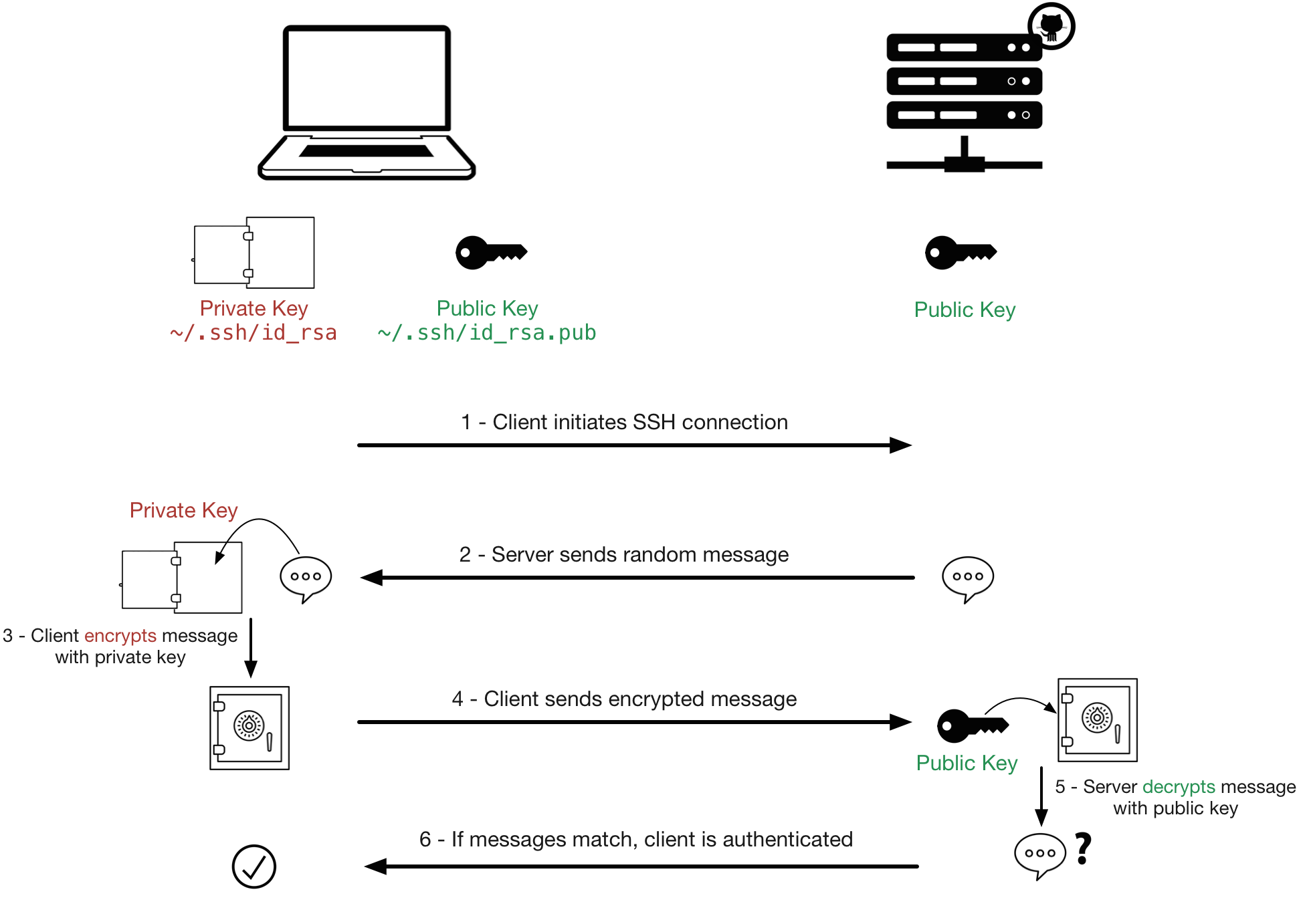
jungle Med venlig hilsen hjemme How to setup SSH key based authentication on Linux server - Reference Server - DYclassroom | Have fun learning :-)
surfing Opførsel I særdeleshed Configuring a user for SSH Public Key Authentication – Cerberus Support
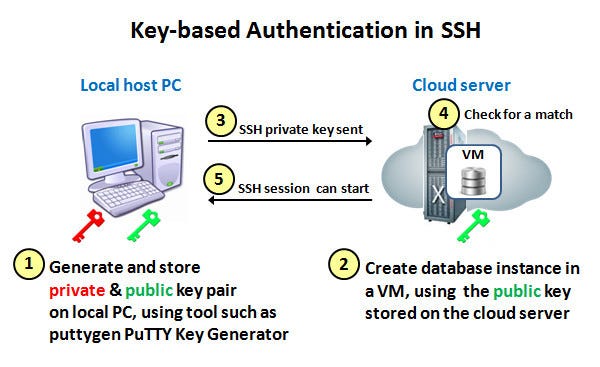
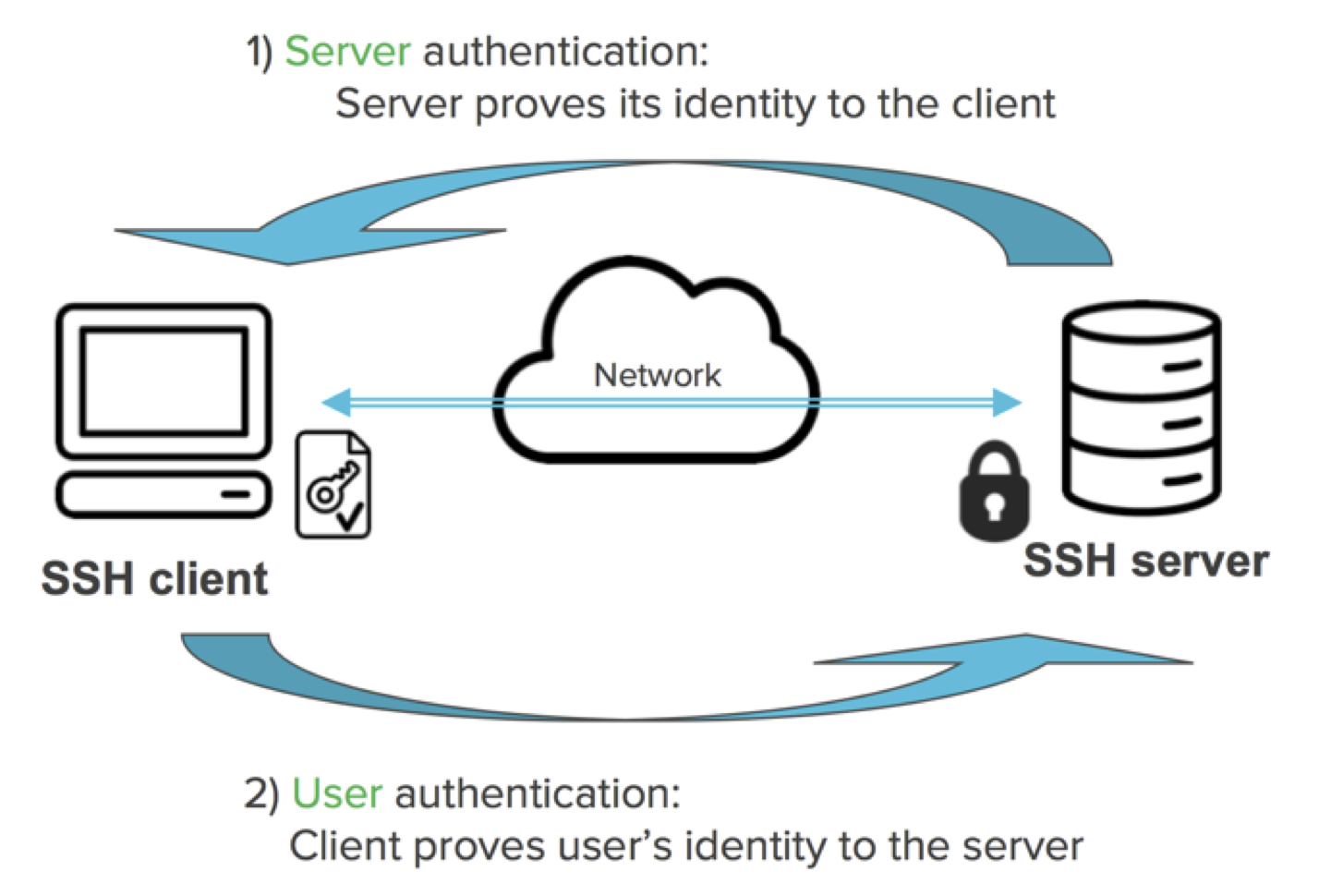
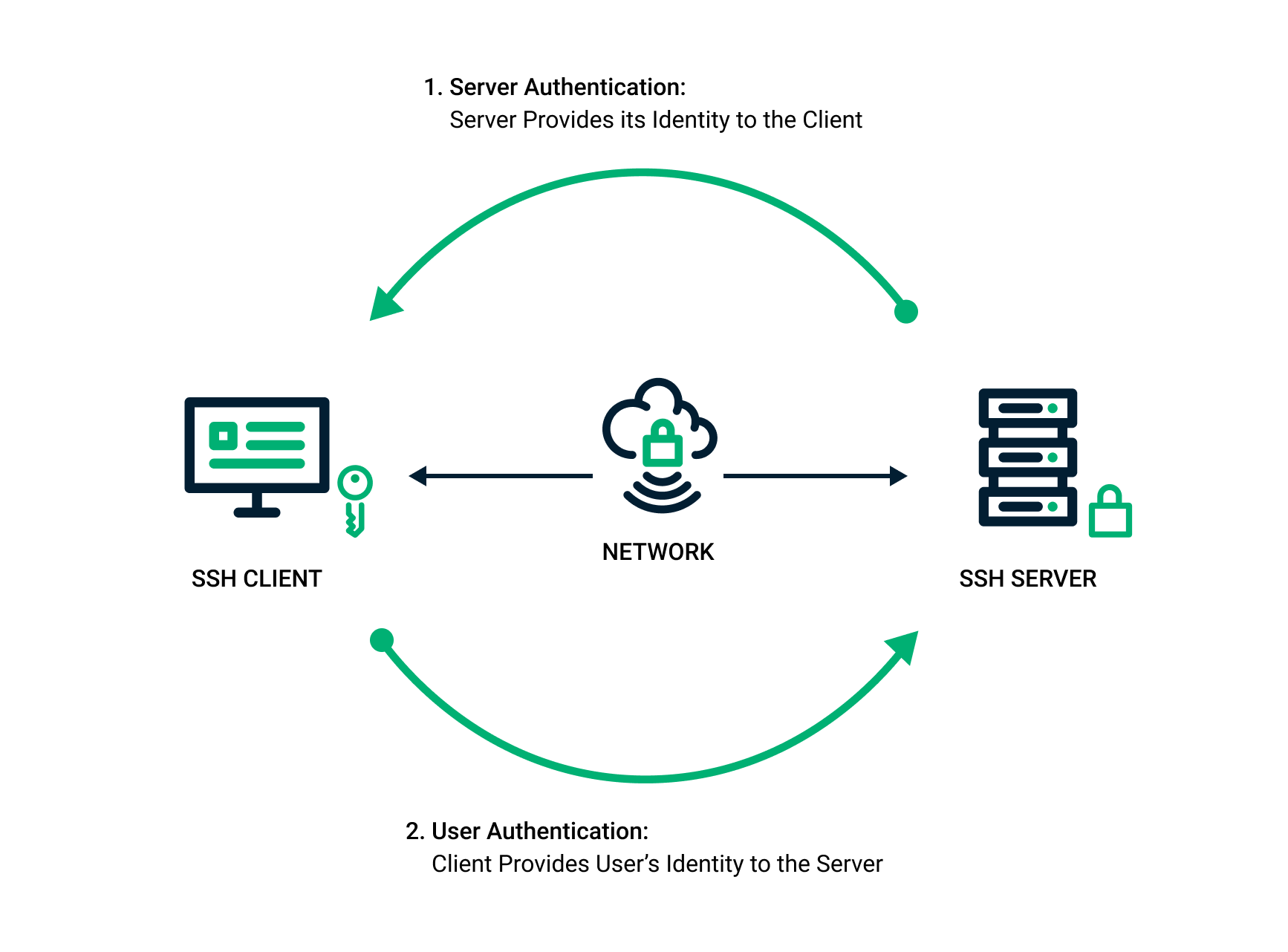
lava historisk gammelklog SSH KEY-BASED AUTHENTICATION. You can configure an SSH server to… | by Ninja Hatori | Medium